Why Salesforce Is Strengthening Security — And What It Means for Currency Updater
Over the past year, Salesforce has significantly increased its focus on security across the platform. This shift has not been arbitrary — it is a direct response to real-world security incidents and the growing sophistication of modern threats targeting cloud applications.
As more business-critical processes depend on Salesforce, the platform has become a high-value target. In particular, integrations, connected apps, and token-based authentication flows have been identified as areas requiring stronger protection.
The Context: A Changing Threat Landscape
Recent security incidents across the ecosystem highlighted common vulnerabilities:
-
Misuse or leakage of long-lived refresh tokens
-
Over-reliance on session-based authentication
-
Insufficient protection in browser-based OAuth flows
-
Weak handling of credentials in distributed applications
These patterns are not unique to Salesforce — they are common across SaaS platforms — but they require proactive mitigation.
In response, Salesforce has introduced stricter guidelines and enforcement mechanisms, particularly around OAuth flows and Connected Apps. The introduction of PKCE requirements and Enhanced Connected App (ECA) standards reflects a broader move toward zero-trust and defense-in-depth architectures.
Salesforce’s Security Direction
The platform is evolving toward a model where:
-
Every authentication flow must be verifiable and tamper-resistant
-
Tokens must be short-lived, scoped, and protected
-
Client-side applications cannot rely on secrets
-
Backend integrations should avoid user session dependency
This is where mechanisms like PKCE and JWT become essential.
Our Response: Strengthening Currency Updater
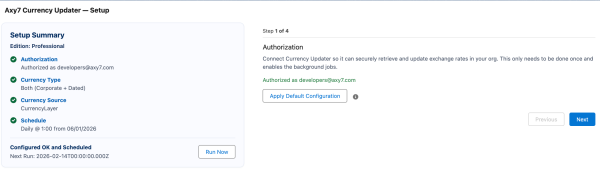
At Axy7, we moved quickly to ensure that all our applications — especially Currency Updater — align with these evolving security expectations.
Rather than applying minimal fixes, we took the opportunity to reinforce the entire authentication model.
PKCE Implementation
Currency Updater now uses PKCE in its OAuth flow:
-
A unique
code_verifieris generated per session -
A
code_challenge(SHA-256) is sent during authorization -
The verifier is required to exchange the authorization code
This ensures that even if an authorization code is intercepted, it cannot be reused.
Importantly:
-
The verifier is never stored persistently
-
No client secrets are exposed in the browser
-
The flow is secure for LWC-based interactions

JWT-Based Server Authentication
For backend operations, including scheduled jobs and bulk updates, we rely on JWT authentication:
-
No dependency on user sessions
-
No reliance on long-lived refresh tokens
-
Secure, signed assertions using certificates
This provides a controlled and auditable authentication mechanism, especially for asynchronous processes.
Encryption and Secure Data Handling
Security is not only about authentication — it also depends on how data is stored and transmitted.
Currency Updater follows strict practices:
Data in Transit
-
All communications use HTTPS with TLS encryption
-
Callouts to Salesforce and external services are fully encrypted
-
No sensitive data is transmitted in plain text
Data at Rest
-
Sensitive configuration is stored in Protected Custom Settings
-
These settings:
-
Are not accessible from client-side code
-
Are isolated per org
-
Are protected from subscriber access in managed packages
-
This ensures that tokens or configuration values cannot be exposed unintentionally.
Server-Side Processing
-
All sensitive operations happen in Apex
-
No tokens are exposed to LWC or browser storage
-
No credentials are included in URLs or logs
Why This Matters for Customers
These changes are not just about compliance — they directly improve reliability and trust:
-
Reduced risk of credential leakage
-
Stable operation of scheduled jobs without session issues
-
Safer integrations across multiple systems
-
Alignment with Salesforce’s future security enforcement
Most importantly, these improvements are transparent. Customers do not need to change their configuration or workflows.
Looking Ahead
Salesforce will continue to raise the security bar, particularly for ISV applications distributed through AppExchange.
By implementing PKCE, JWT authentication, and secure storage patterns today, Currency Updater is already aligned with:
-
Current Salesforce security requirements
-
Upcoming enforcement policies
-
Industry-standard OAuth best practices
Conclusion
Security is no longer a secondary concern — it is a core requirement for any enterprise application.
At Axy7, we see this as an opportunity, not a constraint. By strengthening our architecture, we ensure that Currency Updater remains not only compliant, but also robust, scalable, and trustworthy for all our customers.